43.2 percent of all websites worldwide run on WordPress. This high distribution makes WordPress websites a popular target for attacks. Especially with a small website, many often think they're safe, because who would hack a blog with little reach or no sensitive data? Today I'll show you why this is a dangerous fallacy when it comes to WordPress security.
WordPress is interesting mainly because so many websites use it. For many forms of attack, it is not the "quality" of the hacked targets that matters, but simply being able to infiltrate as many websites as possible in an automated way. What it can look like when a vulnerability is systematically exploited was shown by the example of the vulnerability in WordPress 4.7.1. Countless websites were then defaced on the home page with the notice "hacked by".
The security company Sucuri had found the vulnerability and passed it on to WordPress. And although the problem was fixed in WordPress 4.7.2, millions of sites were hacked in so-called defacement attacks after the exploit became known.
The example illustrates that really every WordPress website is interesting for attacks. Because the attacks run in most cases completely automatically. Today I will show you how such an attack can look like, what the target is and what consequences it can have for you and your website once your website has been successfully hacked.
Your WordPress website should be hijacked
As I said, most of the time it's not even about how big the website is or what's there to get. A large number of websites that have not plugged certain security holes are simply attacked automatically. Once the website is infected, it can be misused to send spam, for example, or even distribute malware to users.
This creates a network of malware suppliers or a botnet that can later be abused for DDoS or brute force attacks. The individual website is therefore often only interesting as part of a larger whole. And the more websites are hijacked or infected, the more valuable the associated malware machinery becomes.
"*" indicates required fields
Number of attacks on WordPress on the rise
The number of attacks on websites is tending to increase. According to Google, 32 percent more sites were hacked in 2016 than in 2015. Brute force attacks were one of the most common types of attack. Simply put, this is an attempt to enter the correct combination of login name and password by mere guesswork.
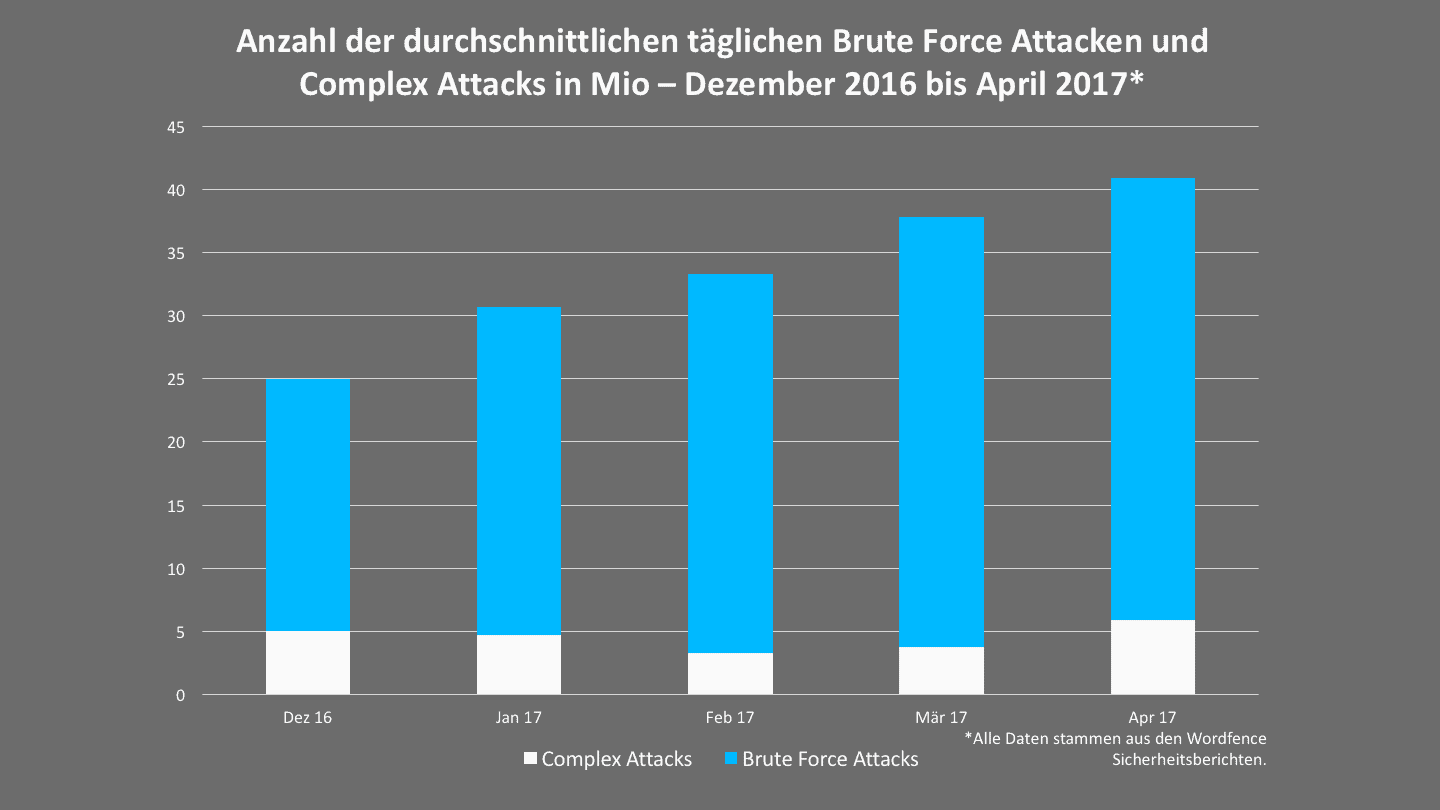
This is also underlined by the figures of the security provider Wordfence . Here, a steady increase of these attacks on WordPress could be recorded in the USA.
Reach is the capital here
The example of a botnet is an excellent illustration of this. A botnet is a network of hijacked websites (which can also be Internet-enabled end devices or routers) that is used to launch DDoS attacks against websites or servers. In the process, the elements of the botnet are activated and bombard the target on command with so many requests that the server collapses and becomes overloaded.
The more websites are included in a botnet, the more powerful and thus valuable it becomes. However, this also means that hijacking WordPress installations is often only the first step. The second step is to create something that can be monetized.
The Three I's: Inform, Identify, Infiltrate
Once a vulnerability is known, the real work begins: A program must be written that can find out if the vulnerability exists and then exploit it automatically. Roughly speaking, non-specific WordPress hacks can be divided into three phases:
Phase 1: Obtain information
The first step is to search for knowledge about known or unknown vulnerabilities in WordPress. This is possible via platforms such as the WPScan Vulnerability Database.
For the defacement attacks I mentioned at the beginning of the post, just looking at wordpress.org would have been enough.
Phase 2: Identify attack vectors
Now we know where to start. In phase 2, a script must be written that makes it possible to pick out those websites from the mass of websites that have the vulnerability. In the case of the defacement attacks on WordPress 4.7 and 4.7.1 in 2017, this was easily possible by reading the WordPress version.
Phase 3: Automated attacks
Once found, the website can be (automatically) hacked to make the (un)desired changes. Some typical examples are:
- Data theft: Attempts are made to steal sensitive data from your website or users. This can be e-mail addresses or bank data - but in principle anything that can be sold or reused is interesting. For example, a fake form can be placed on your website that steals all the data entered. And this in a completely trustworthy environment and even encrypted with SSL.
- Website hijacking: Your WordPress website will be included into a botnet. This secures control over your website and makes it possible, for example, to launch DoS or DDoS attacks against it on command.
- Injecting malicious code: Mal icious code is placed on your website. For example, your advertising space can be misused or data can be stolen by using false forms.
In most cases WordPress hacks cost time and money
What costs arise from a WordPress hack and what direct or indirect consequences an attack can have exactly, can not be said in general terms. But you have to be prepared for these three consequences with hacked websites:
1) Costs for restoration
Millions of attacks on WordPress websites take place every day. The plugin manufacturer Wordfence alone measures an average of 35 million brute force attacks and 4.8 million exploit attacks daily for April 2017. In other words: there is no absolute security. You can only keep the probability of being hacked as low as possible and create appropriate mechanisms that allow you to quickly restore your website if the worst happens.
In the best case, you have a backup of the website and can simply restore it. If the backups are also infected or it is not possible to restore them, it becomes more complicated. Then you have to spend time and money on manual removal of the malware.
2) Loss of turnover
Depending on what kind of malicious code was injected and how long your website needs to be maintained, you may also incur costs in the form of lost revenue from advertising and sales.
3) Loss of trust
Google sees everything: A hacked website often contains malicious code that spreads malware. If Google detects this - and you do nothing about it - your website ends up on a blacklist. When users access the site, they will see a security notice warning them about malware or phishing. This can also lead to your Search Engine Ranking Position (SERP) suffering and you losing significant reach.
Conclusion: Attacks on WordPress websites are quite normal
Of course, this article is not intended to stir up unfounded panic. But what it should make clear: Just because you have a "small" website doesn't mean you shouldn't actively address the issue of WordPress security.
For example, it is important to know that the majority of vulnerabilities can be eliminated through regular updates. And that an SSL certificate does not protect your website from attacks.
At the outset, I mentioned that the sheer proliferation of WordPress as a CMS makes every website a potential target. But this spread also brings a decisive advantage: A worldwide community works around the clock to make WordPress more secure. And so for every vulnerability and for every problem there is sooner or later an adequate solution.
