Having your website targeted by shady characters - that's a horror scenario. Unfortunately, today it is becoming easier and cheaper to use services to make websites inaccessible to normal traffic. DDoS attacks in particular are on the rise.
The danger of a DDoS attack applies to all websites, and you should be aware of it too. The abbreviation stands for "Distributed Denial of Service" and is also referred to as a "distributed network attack". In this case, the server and other network systems of a website are deliberately overloaded by requests from many devices and brought to their knees.
Attacks of this type are unfortunately a widespread threat. The better known your website is, the more likely it is that someone will try to damage your sales or reputation through a DDoS attack. This can be devastating - especially if you don't know what's going on or how to deal with it.
In this day and age, it is also becoming easier and cheaper to buy DDoS services. That's why companies and websites are more at risk than ever. With the right precautions, DDoS attacks can be prevented or even stopped in their tracks.
What are DDoS attacks?
A DDoS attack is a sudden influx of artificial traffic designed to cripple a website's server. When your server receives more requests than it can handle, it slows down or crashes - so no one can load your website.
By comparison, a normal Denial of Service attack (DoS attack) can originate from a single source. In contrast, a DDoS attack consists of a large volume of targeted requests from dozens, hundreds, or even thousands of individual devices. These are usually hijacked computers that have been hacked and are secretly running malicious software in the background. Together, these devices form a botnet or zombie network.

Botnets are not limited to computers and phones, however. Tablets, surveillance cameras, or even household appliances such as Internet-enabled dishwashers, televisions, or baby monitors (which are often poorly secured or not secured at all) can also form a botnet.
This is also what makes a DDoS attack so perfidious. Because they involve real devices at different locations, they appear as normal accesses and are difficult to distinguish from real clients - even during an active attack.
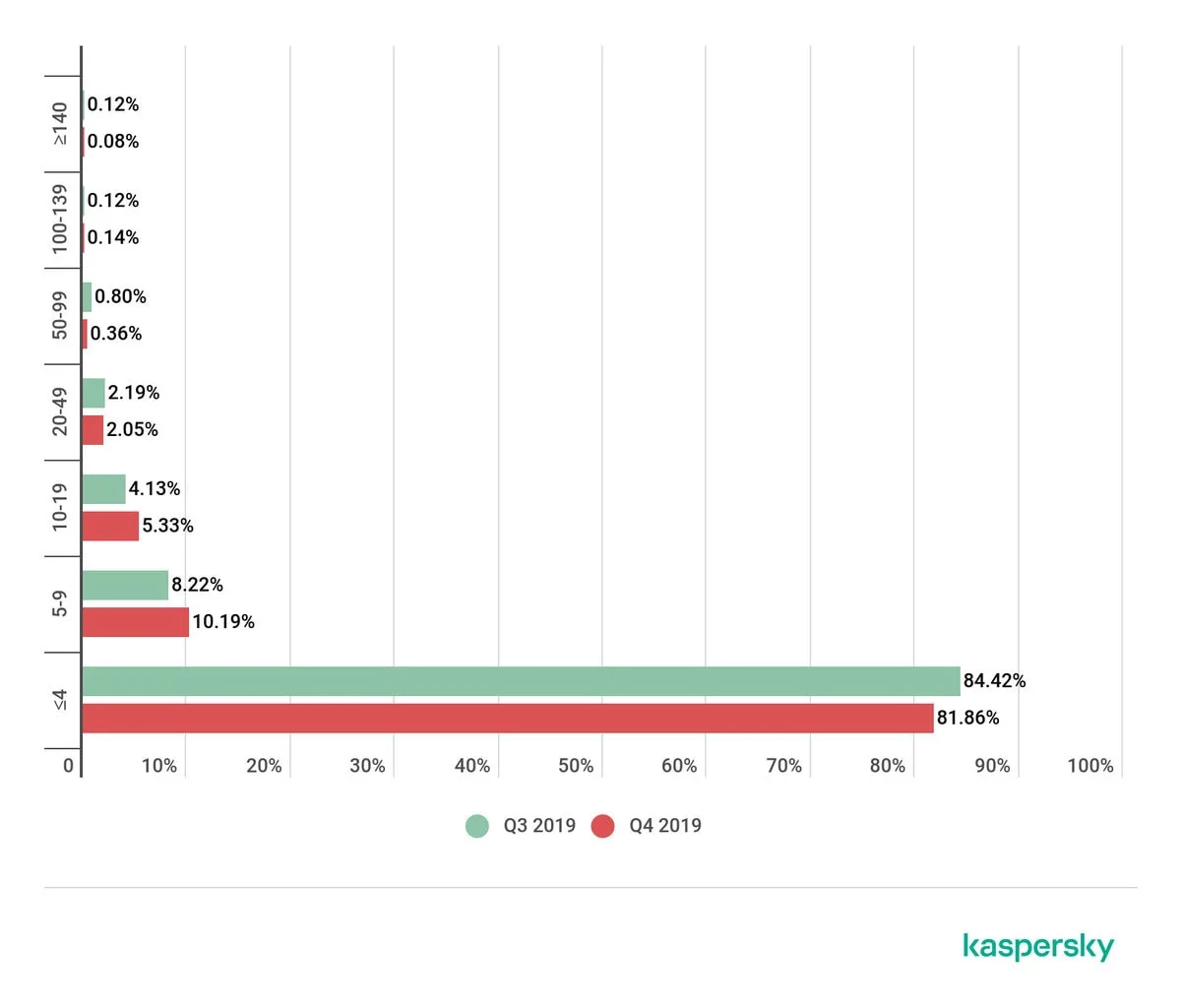
DDoS attacks usually last a few hours at most. In severe cases, however, they can last for days. The longest DDoS attack ever lasted 509 hours, or almost 21 days. However, even the extreme cases usually resolve themselves within a day or two: More than 80 percent of attacks last less than four hours. More than 90 percent are over after nine hours at the latest.
What happens during a DDoS attack?
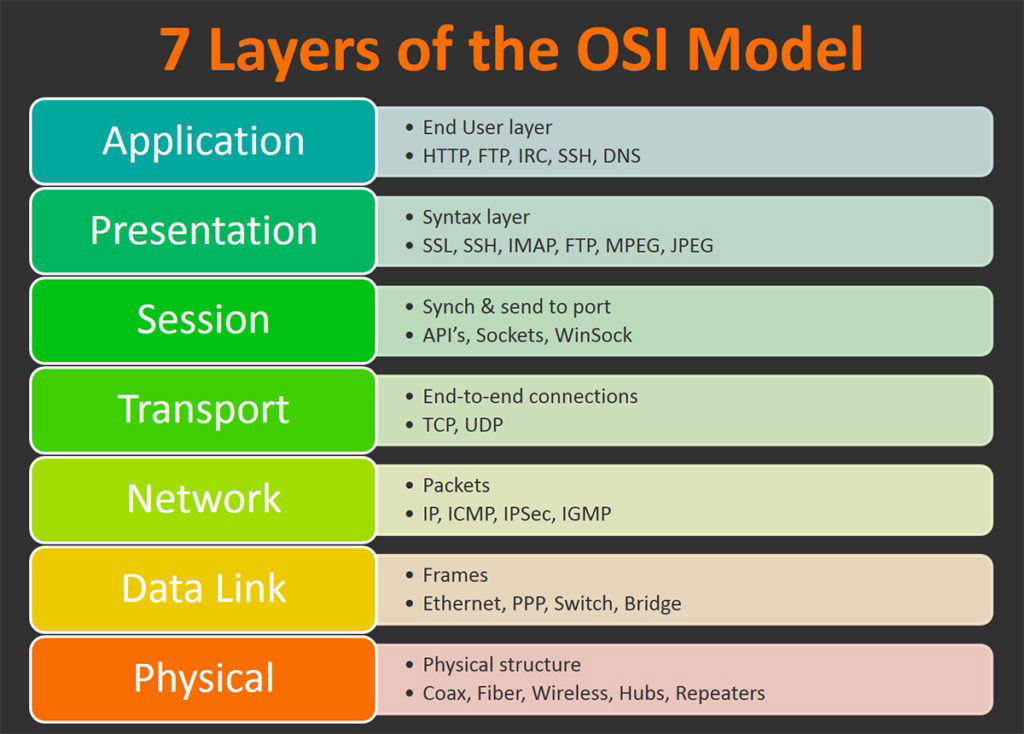
Network resources such as web servers can only handle a certain number of requests at a time. The bandwidth of the server's Internet connection and other layers of the network is also limited.
Various attack points can therefore be attacked - even simultaneously. The more complex the offense, the more difficult it is to distinguish the attack traffic from normal requests. As a consequence, countermeasures may be less effective.
As soon as the number of requests to the network components exceeds the capacity limit, your website immediately starts to falter. Loading times increase, and it takes longer and longer to call up the website. Eventually, the server may even crash altogether and stop responding to requests altogether. If your WordPress user interface or server administration such as cPanel are also located there, you will then also no longer be able to log in and access them.
Worse, however, is the aftermath of a DDoS attack: For affected companies and organizations, it can mean considerable economic damage. Depending on the time of sale, the fact of being unavailable for a few minutes can quickly cost tens of thousands of euros in lost profits.
The loss of image should not be underestimated either. 88 percent are less likely to return to a website after a bad experience - such as extremely long load times. Not only do you miss out on potential new customers (who may never return), but your regular customers are likely to be upset and blame you for the downtime.
If you don't manage to quickly talk to your host to get them to shut down the server, you could end up sitting on terabytes of expensive bandwidth overages.
The good news: DDoS attacks can have enormous consequences, but they usually do not pose a direct security risk. Your website may be taken offline, but credentials such as usernames are not automatically compromised.
"*" indicates required fields
Why are websites targeted by a DDoS attack?
There are many reasons why you could be attacked. However, the goal is always to make your website inaccessible to others. This can happen for various reasons:
- In response to a controversial statement on your part or to a company decision with which someone disagrees (hacktivism).
- Your economic competitors may decide to shut down your website during an important sales time, leaving only their website accessible.
- To damage your reputation.
- To distract your IT staff while your website is broken into. (This is a rare case where DDoS attacks can actually be dangerous).
- To demand a ransom.
- Or out of boredom.
It is surprisingly easy and cheap to rent a botnet and shut down a website for a short time. Others have already done the groundwork and now anyone can buy their services temporarily.
As a result, the frequency and strength of DDoS attacks has increased sharply over time. Whatever the motivation behind it, easier access is an important incentive for smaller DDoS attacks. Fortunately, these are the easiest to stop.
How to prepare for DDoS attacks
Being prepared is the best remedy against attacks of this kind. Develop a worst-case plan before anything happens. The question is not necessarily if, but when an attack on your website will occur. Therefore, better safe than sorry. Here are a few tips on how to avoid DDoS attacks.
Formulate a contingency plan
As mentioned earlier, the best way to counter this threat is to be prepared. Sit down with your IT team so everyone knows exactly what to do if the worst happens.
DDoS defense contingency plan
Create a contingency plan that outlines exactly what everyone has to do in the event of a DDoS attack: Who is responsible for IP blocking? Who contacts the web host and security providers? Who monitors how and where the attack takes place?
Also be prepared for an influx of complaints via phone, email and social media. People will want to know what's going on and why they can't access your site. Consider how to automate as many of these interactions as possible, as all eyes will be needed elsewhere for the duration of the attack.
Choose Managed Hosting
If you don't have a team of experienced IT professionals that can deal with this issue, managed hosting is the next best option. Choose a host that offers DDoS protection measures. This way, he will take care of everything technical to protect your website and get it up and running again as soon as possible.
It is important to do thorough research. Ask your web host if they offer DDoS protection, what exactly they do during an attack, and how they handle bandwidth overage charges.
Set up uptime monitoring
Automatic monitoring of your website's uptime is a crucial early detection method. An uptime monitoring service notifies you via email and push messages within minutes if your website crashes or slows down significantly.
Your web host may offer this service out of the box. If not, there is a paid professional solution with Pingdom or a free one with Uptime Robot that pings your website every five minutes. Another solution is Uptrends.
Use a firewall and a Content Delivery Network (CDN)
A web application firewall (WAF) is one of the best defenses against a DDoS attack. It sits between your website and the requests and filters the network traffic to exclude malicious access. By doing this, it not only helps protect against attacks, but can also contain DDoS attacks by limiting requests.

If sophisticated technology is not used in the attack, the DDoS attack may not arrive at your website at all. Even if partially successful, much of this traffic will be eliminated.
To set up a firewall, you can try a service like Cloudflare or Sucuri. You can find more providers here.
A CDN, or Content Delivery Network, can also help you with this - because a website that uses such a network is a bit harder to take down. With a CDN, copies of the website reside on different servers in different locations.

This way, a comeback after heavy load is easier. However, it is not a fail-safe solution. If your main server is directly attacked, a CDN can only reduce the impact, not stop it. Still, it's a good investment, especially since many services bundle both a CDN and DDoS protection in their packages.
What to do during a DDoS attack?
Whether you're reading this when the baby's already dropped in the well, or just to prepare yourself for the worst-case scenario: Here are a few tips on what to do if your site comes under attack. You can't always do anything to stop a DDoS attack, but you're not completely powerless either.
1. Don't panic
It can be scary to receive an email saying your website is down. A mailbox full of complaints is equally unpleasant. You try to visit your site or log in - and it just refuses to load. Panic sets in.
But even if it is an unpleasant situation, DDoS attacks are not dangerous per se. Your data is still safe, your login has not been hacked. Of course, you should be vigilant and make sure that in all the excitement no one tries to brute force your administrator account. But a DDoS attack alone is only a threat to your reputation and nothing else.
Regardless of whether you're prepared or you're dealing with it now for the first time: At a certain point, there's nothing to do but wait. A DDoS attack costs attackers money and resources, so it won't last forever.
Only very large and prominent companies are likely to be subjected to protracted attacks. Chances are, it will all be over in a matter of hours. Follow the steps below and don't stress about anything else.
2. Tell your web host
In case of a DDoS attack, you should contact your web host - as soon as possible - to inform them about the situation. If you haven't already done so, ask him about overdraft fees and DDoS protection measures. If he offers something like that, he will quickly get to work to stop the attack.
Even if this is not the case, you will know what (if anything) the attack will cost you. Also, the provider can shut down your server if the situation lasts too long.
Bandwidth overages can be expensive and traffic from hijacked computers flows quickly. Talk to your host as soon as possible and - if you haven't already - look for one that offers DDoS prevention and emergency services as a package.
3. Set up a CDN and a firewall
If you don't already have a CDN and firewall set up on your server, now is a good time to do so. Security service providers will be happy to help and will often work directly with you to block the malicious traffic immediately.
Sucuri and Cloudflare are the two most popular DDoS prevention services. Once you have them up and running, their automatic measures should kick in immediately and reduce the impact of the attack. In German-speaking countries, there's also Akamai.
If you don't see any results, enable Cloudflare's "Under Attack Mode" or contact your provider and ask for additional support.
4. use geoblocking and IP blocking
You can also improve the situation manually by blocking IP addresses that do not belong to real clients. IP addresses are the individual identifiers given to each device on the Internet.
If a certain IP visits your website dozens, hundreds or thousands of times during an active attack, simply block it. Then it won't be able to do any further damage and will simply be rejected. This way you can fix part of the problem yourself. Your web host may also offer an IP blocker for such purposes.
IP Blocking function at Raidboxes
Alternatively, you can simply use the IP blocking function of Raidboxes. You can find it in your Box settings.
Geoblocking is also a good solution. Here, IP addresses from entire parts of the world are blocked across the board. This is very good if a lot of the traffic comes mainly from certain countries. This feature is part of many WordPress security plugins. There are also extensions like IP2Location Country Blocker that can be used specifically for this.
IP blocking is not always effective - or not effective for very long - as it may simply change the IP address and flood your website with requests again. But it is worth a try.
Web application firewalls perform many of these functions automatically. However, you can also look here to see if it is possible to block proxies, turn on access restrictions, or enable existing IP access control lists.
Conclusion: Effectively prevent DDoS attacks
Unfortunately, if someone is determined enough and has the necessary resources, it is impossible to stop them from launching a DDoS attack against your website. However, this doesn't mean that you should just sit back and do nothing. You can take various measures to prevent the majority of smaller attacks and minimize their consequences.
Even if a person really wants to take revenge on your company, they won't be able to keep it up for long without paying exorbitant amounts of money. Compared to the damage done, it's usually not worth it. Eventually, every DDoS attack must come to an end - even if it's only when the person gets bored.
A firewall, a CDN and a quality web host are your best bet to prevent DDoS attacks. Take precautions before the worst happens. And have a plan in place so you and your team can get everything under control as quickly as possible.
If you are interested in more IT security topics, feel free to read our articles on Brute Force, Cross Site Scripting and Cross Site Request Forgery.
What questions do you have about DDoS attacks?
Feel free to use the comment function. You want to be informed about new postsand tips for more security? Then follow us on Twitter, Facebook or via our newsletter.
